Discover How to Choose Between HDD, SSD, and Cloud Storage. Which Is Right for You?
#Data Storage
#Cloud Storage
#data management
#cloud services
#data backup
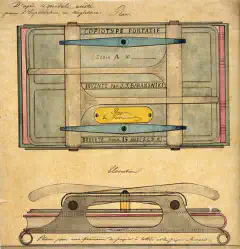
Unlock the Secrets to Advanced Copy Functions in OS—What’s the Fastest Way?
#Operating System
#data management
Learn how to effortlessly turn your Linux system into a high-performance NAS server for seamless file sharing and management.
#network-attached storage
#Server Configuration
#data management
#Home network
#data backup
Discover the ultimate file sync solution between SyncThing and FreeFileSync. Effortless data management for all your devices.
#Comparison
#data management
#Open Source
#privacy
#security
Learn how to securely back up and restore files using Robocopy, a powerful tool for data protection and peace of mind.
#Backup and Restore
#Data protection
#data security
#Cybersecurity
#IT solutions
Explore the comprehensive comparison of Synology, Terramaster, and Qnap NAS systems, uncovering their features, performance, and data security.
#data management
#Performance
#data security
#virtualization
#Data Redundancy
Explore the top NAS operating systems in this comprehensive comparison to discover the perfect solution for your data storage requirements.
#Data Redundancy
#network-attached storage
#Operating Systems
#Data Storage
#data management
Discover the power of OneRep’s data removal service in safeguarding your privacy and personal information online.
#online privacy
#Personal Information Protection
#data security
#Cybersecurity
#identity theft
Discover the value of free Oracle certifications for cybersecurity and IT professionals, and explore the opportunities they offer for career advancement in Oracle Cloud Infrastructure (OCI).
#Cybersecurity certifications
#IT certifications
#career advancement
#professional development
#Online Learning
Discover the true nature of unclassified information, its key characteristics, safeguarding measures, and relevant regulations for effective protection.
#information security
#Data protection
#information management
#Access Controls
#Encryption